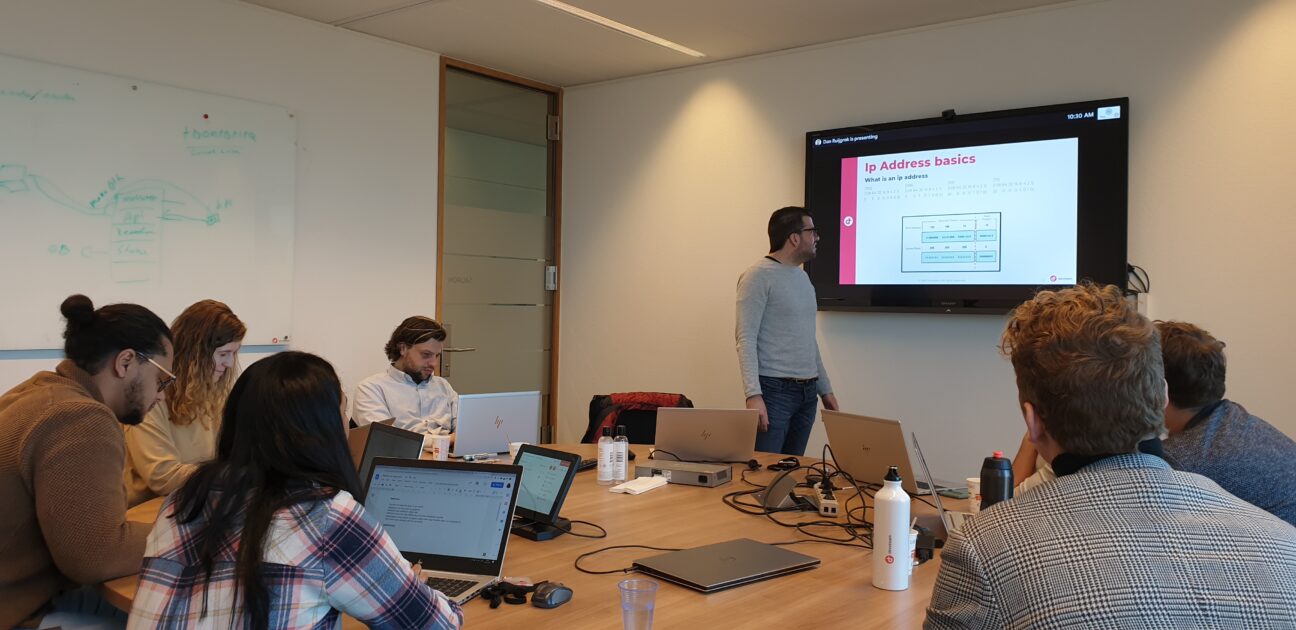
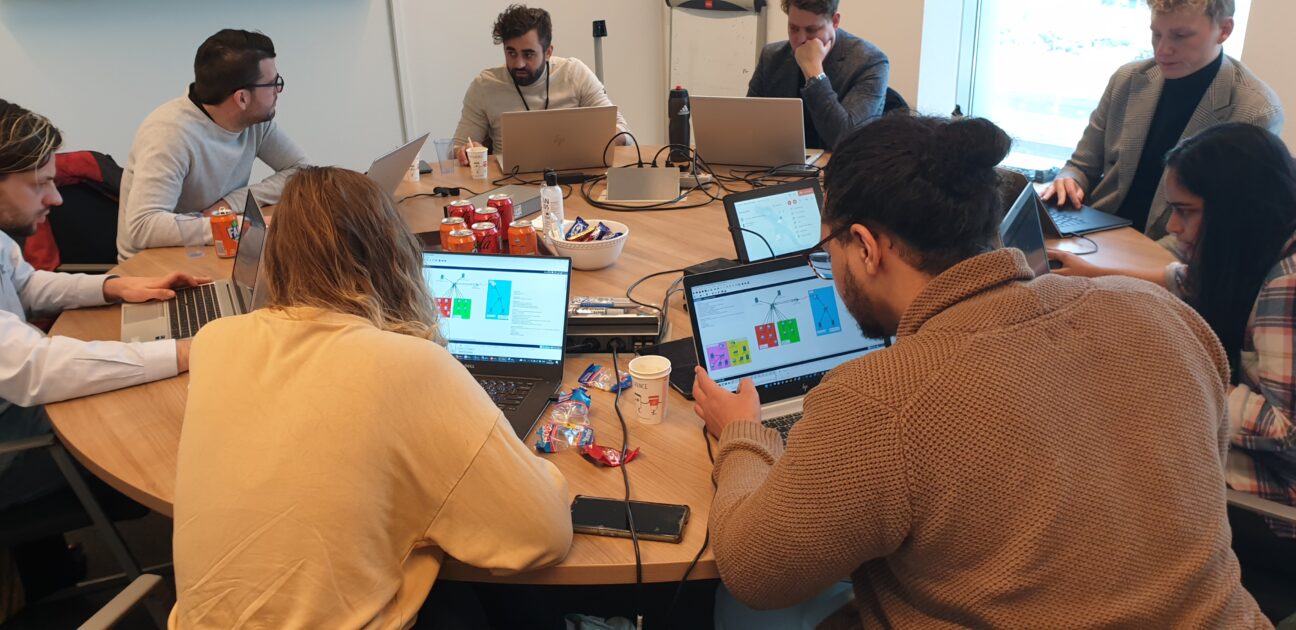
During the Futures traineeship, we’ve had the opportunity to attend a network training session. Because of the measures taken against COVID-19, this was continuously postponed, but eventually, we had the opportunity to join (yes, we all tested and kept our distance). In this workshop, we went over the basics of networking. The subjects we’ve covered included, but were not limited to the OSI model, switches, IP addresses, DHCP, Routers, NAT, and many more. To give a glance at the information we’ve covered, a little summary is given about 3 topics that, according to me, were the most useful.
3 key takeaways from the Networking Session
1. IP addresses and subnets
During the workshop, we’ve learned that an IP address consists of 4 numbers, separated by periods. This ranged from 0.0.0.0 to 255.255.255.255. The first 3 of these numbers are dedicated to the network portion of the IP address, while the last number is dedicated to the host portion. Since a network can consist of thousands or even more connected devices where each device has a dedicated IP, it is often useful to use subnets. This is because subnetting narrows down the IP address to usage within a range of devices. One can, for example, state that a certain subnet is dedicated to the sales department of a company, and another subnet is dedicated to the IT department. It is then possible to configure that the sales department of the company has no access to the IT department.
2. Firewalls
It is important to secure your network as well. That is why there was also some time dedicated to firewalls. Firewalls can either accept, reject or drop connections into a network. One can for example accept new and established incoming traffic to the public network interface on ports 80 and 443 (HTTP and HTTPS web traffic). But if you don’t want non-technical employees to connect to your network, you can drop or reject IP addresses in a (office) network to port 22 (SSH).
3. Proxy servers
Another subject covered during the workshop was proxy servers. We learned that a proxy server is any machine that translates traffic between networks or protocols. It’s an intermediary server separating end-user clients from the destinations that they browse. Furthermore, it was mentioned that proxy servers provide varying levels of functionality, security, and privacy depending on what is needed. Most, if not all people have been in contact with a proxy server, since for example, a company can decide to prevent employees from accessing certain sites that are not secure. Moreover, it can also cause bandwidth savings so that the loading times are reduced. In summary, proxy servers are an amazing way to secure a network.
About our traineeships
Learn more about our Young Professional career opportunities in the wonderful world of IT and our academy: the Devoteam Futures. Discover how we help you grow with our IT traineeship, which growth paths there are, and what other Young Professionals think about their development.