In the first installment of this Axway API Management for business focused series, we have covered the Axway’s API gateway architecture, its key components and their functions.
We recommend you to read the two previous blogs as well:
- Click here to read Axway API Management – An Introduction (part 1)
- Click here to read Axway API Management – Policy Studio (part 2)
In this (third) installment, we will deeply dive into the API caching, protecting and security mechanism and troubleshooting proces.
Caching
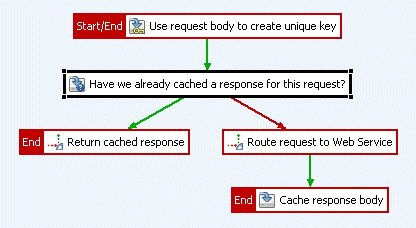
The Axway API Gateway platform provides capability to store the response as a cache into its database as well as in memory. The in memory cache is provided by EHCache as a distributed caching mechanism across multiple api gateways deployed for the organization. There are multiple levels of caching possible.
Cache Levels
Multiple levels of caching can be enabled depending on the organization’s needs.
- Local Cache – Local caches are used where a single API Gateway instance has been deployed. Cached data will be stored in memory.
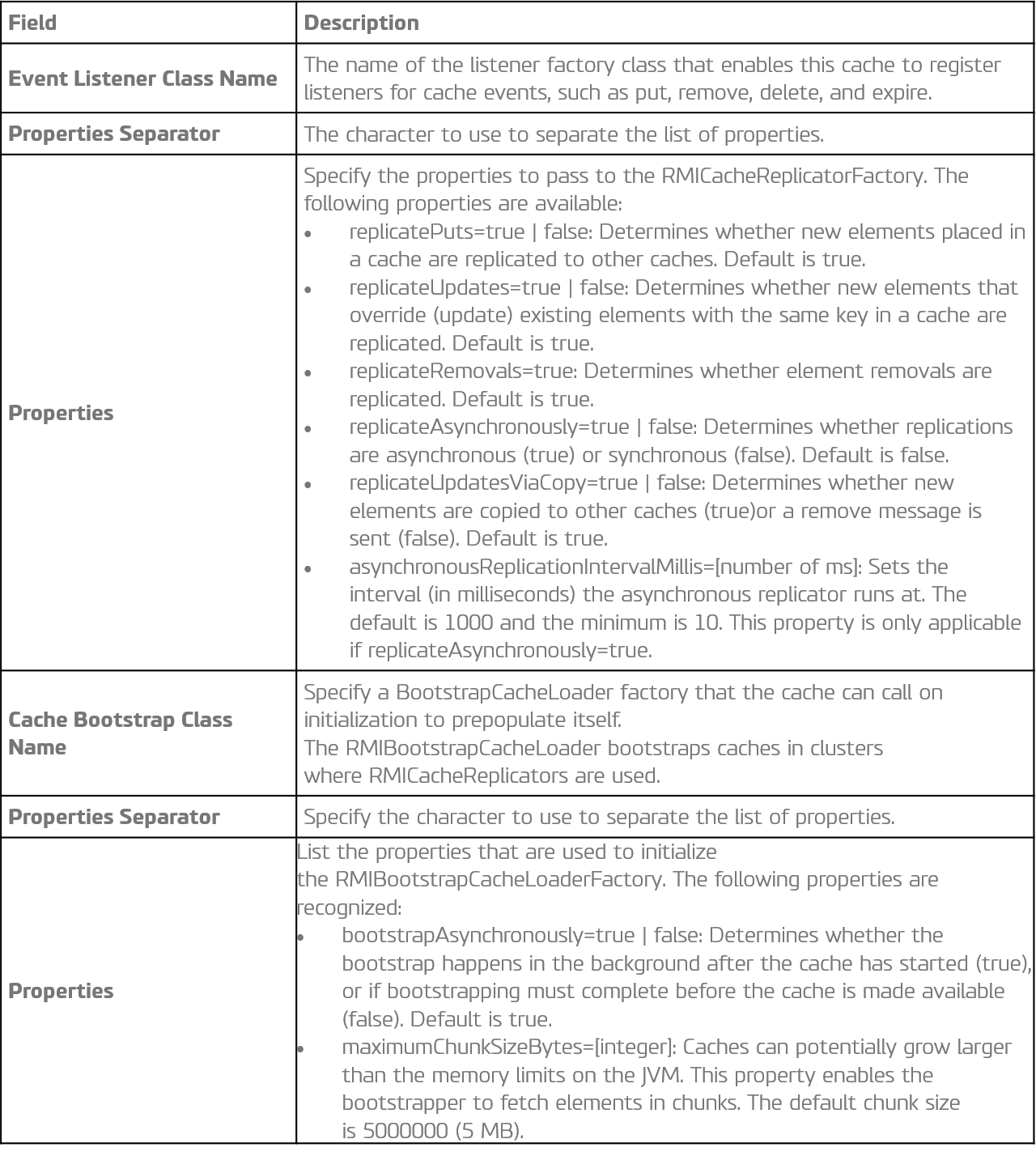
- Distributed Cache – Distributed cache is the mechanism where the cached data is shared across multiple api gateway instances. Each of the API gateway will have its own local cached data but registers a cache event listener that replicates messages to the other local caches so that put, remove, expiry, and delete events on a single cache are duplicated across all other caches. This is effective to really enforce the policies like throughput, concurrency for a particular API where the consumer can use multiple gateway to channelize the call. In a distributed cache, there is no master cache controlling all caches in the group. Instead, each cache is a peer in the group and needs to know where all the other peers in the group are located. Peer Discovery and Peer Listeners are two essential parts of any distributed cache system.
Configuration
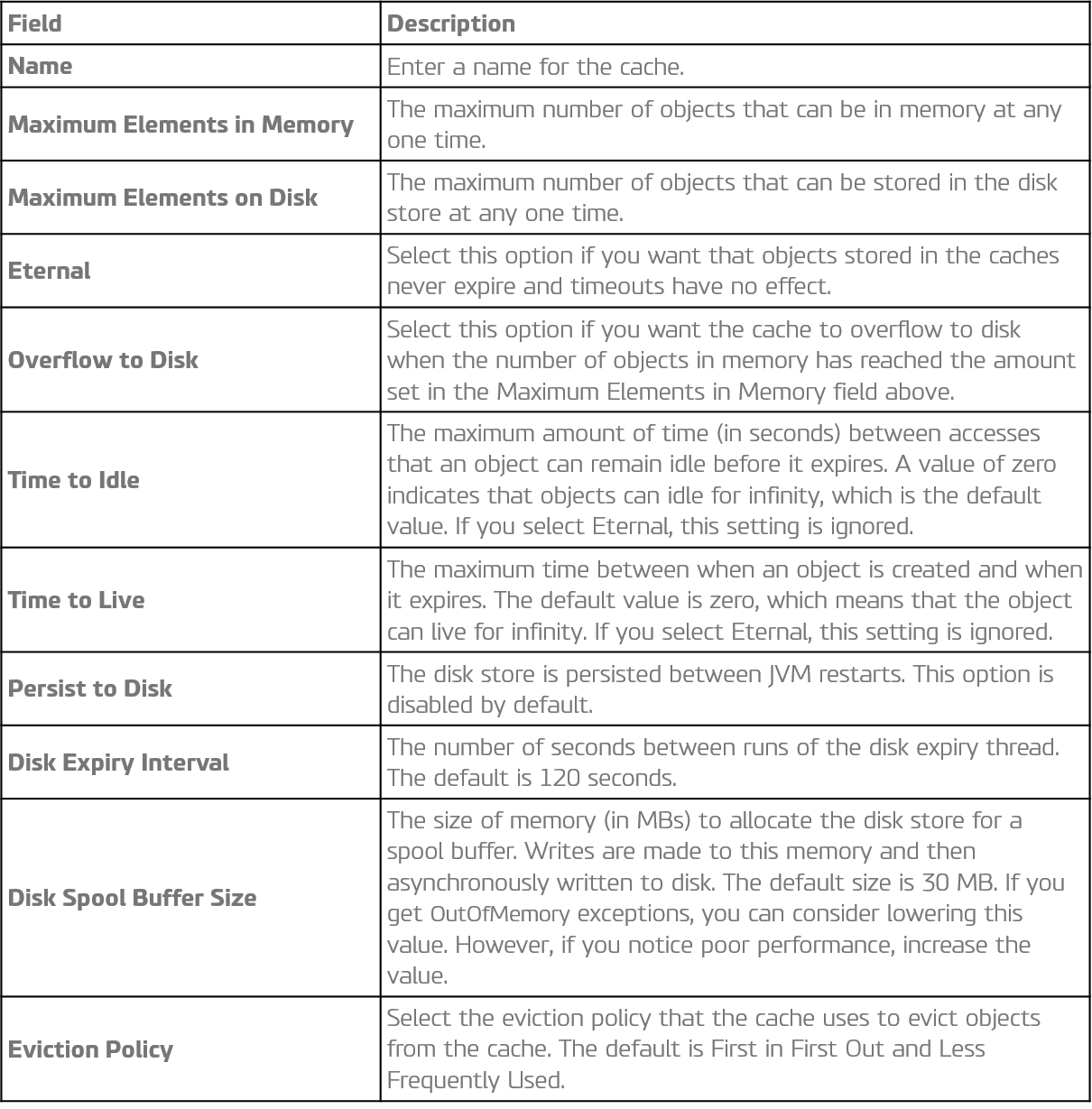
In addition to this, the below parameters are used for distributed caching.
Protection and security
An Axway API Management business platform provides a robust framework to protect the APIs from external threats and security breaches. Lets have a look into the capabilities they provide.
- Threat Protection: Axway API Gateway Management platform offers protection against attacks such as the Denial of service (DOS) , Distributed Denial Of Service (DDOS). Apart from this, the platform offers out of box capabilities to protect from SQL injection, Identify Spoofing, javascript injection, content filtering and XML/JSON validation
- Security – Authentication And Authorization: In terms of protecting the API getting accessed by untrusted or unauthorized sources, Axway provides both out of the box as well as third party integrations with Oauth provider or Identity access management systems. The API management platform provides the following capabilities:
- Support to Oauth 2.0 both 2 legged and 3 legged flows
- Oauth 2.0 with grant types – Resource Owner Credentials, Client Credentials, Implicit, authorization code
- Encoded basic authentication
- HMAC – signed / unsigned both
- Api_key
- Supporting SAML based authentication and authorization
- Open ID connect
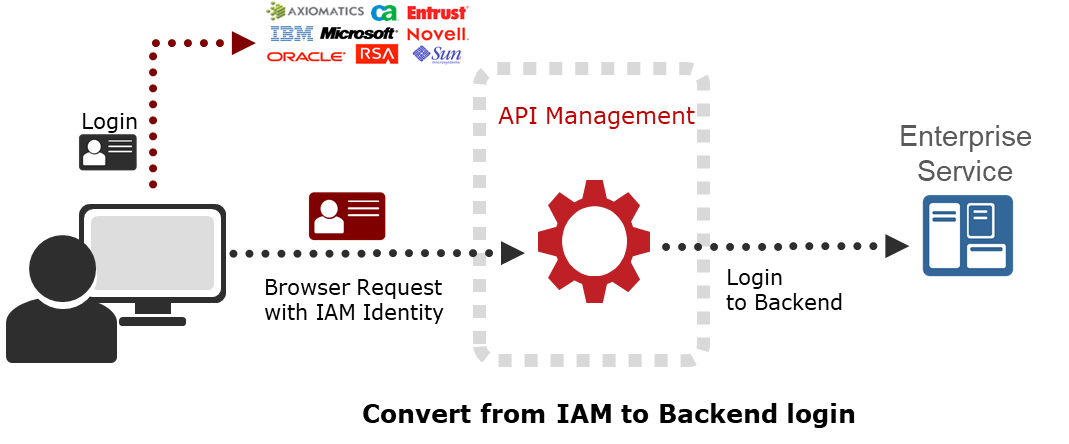
Apart from the above capabilities, the platform offers seamless integration with third party identity access management systems (IAMs). Integration with third party IAM(s) gives the flexibility to separate out the manageability user lifecycle management to the desired platform and thus API management platform validates and authorize the user to access the api based on the token issued by the IAM platforms.
Troubleshooting
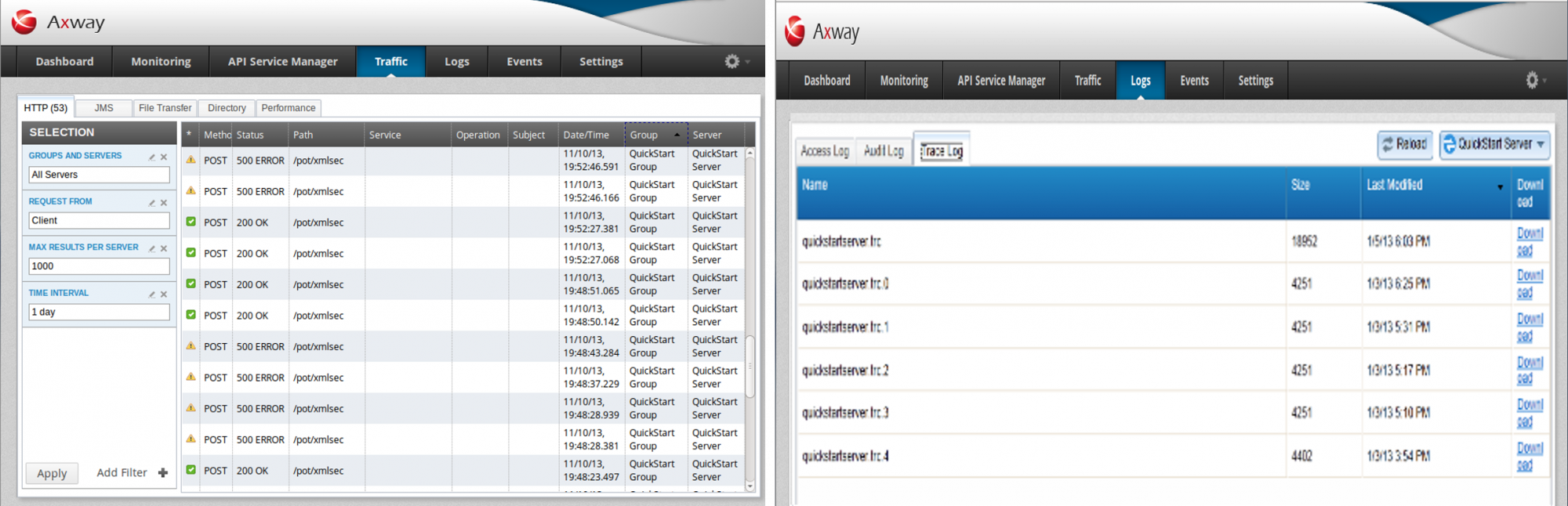
Axway API Management business suite comes up with web based GUI administration console, more popularly known as API Gateway Manager which helps in troubleshooting the API. API Gateway Manager helps in creating different sets of dashboards, therefore monitor the traffic and perform the root cause analysis at the level of the domain, api gateway instance, service, remote host and client.
Following are the key KPIs that can be monitored and can be analyzed further.
System Resource – Monitor the following metrics:
- CPU Usage : Average amount of CPU used by the API Gateway instance.
- Memory Usage : Average amount of memory (in MB) used by the API Gateway instance.
- System Memory Usage : Average amount of memory used on the machine hosting the API Gateway. This includes memory used by the API Gateway and all other processes running on the machine.
Along with this metrics, the peak usage for each of the KPIs can be monitored.
API Resource – Monitor the following metrics:
- Success: Number of successful API calls made with http status as 200.
- Failure: Number of unsuccessful API calls made with http status as 300,400 and 500 series. The numbers can be categorized based on the error statuses.
- Policy Violations – Violations of the policies like throttling, transactions per seconds.
- Security Violations – Violations of the security policy like invalid token, expired token, oauth validation failed.
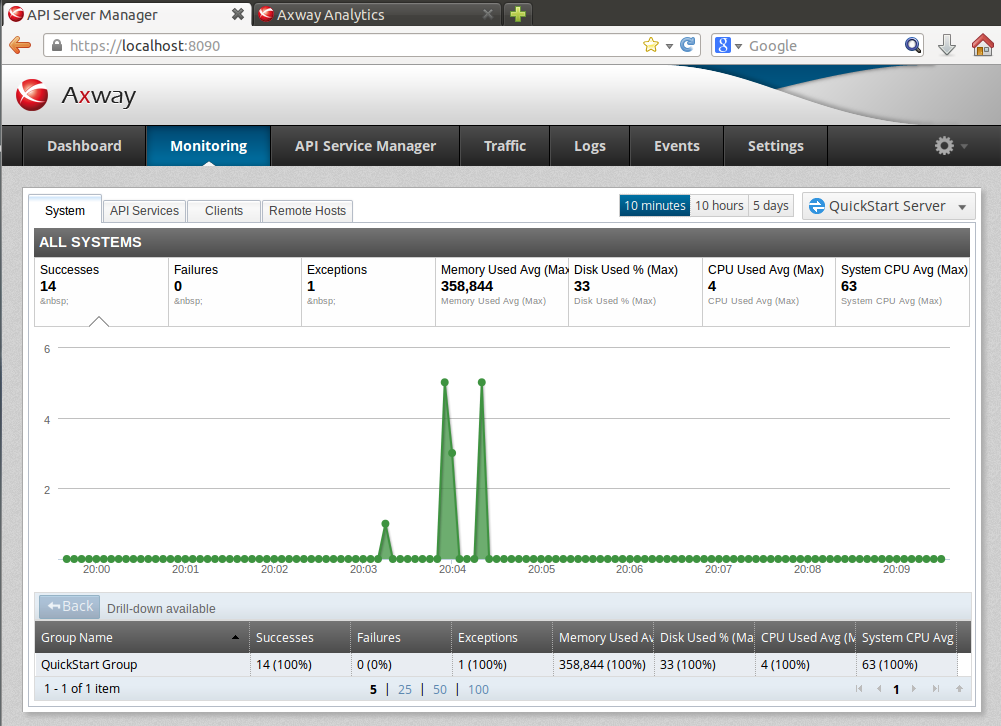
For each of the KPIs further drill down can be done to pin point a particular request under the problem.
Detailed auditing of the logs, individual request response, alert, notifications, and logs helps to do the root cause analysis of the issue.
 Next API Management for business blog
Next API Management for business blog
In the following blog installment we will touch up on the deployment, analytics and setting up the developer portal to engage communities, partners and developers.
For questions about this blog you are able to contact Arijit Roychoudhury, Integration Architect at Devoteam Netherlands (arijit.roychoudhury@devoteam.com). If you are interested in API Management as a solution for your business, feel free to contact Ratko Popovski, manager Architecture & Implementation at Devoteam Netherlands (ratko.popovski@devoteam.com).

